Keystorm
Computer Club traditionally runs a PGP keysigning party each year, to promote good privacy and security habits among the CMU population. Logistically, keysigning parties are a little tricky: you need to put together an authoritative master list of submitted fingerprints for verification during the event, and then there needs to be a reasonable way to get ahold of the keyring once it’s over.
In the past, we had accomplished this through the awkward practice of having all attendees literally handwrite fingerprints on a chalkboard. Usability issues aside (you try and find two dozen CS majors all with quality penmanship), this does nothing to address the keyring problem. We handled this manually, requiring guests to email in pubkeys and then applying liberal usage of cat.
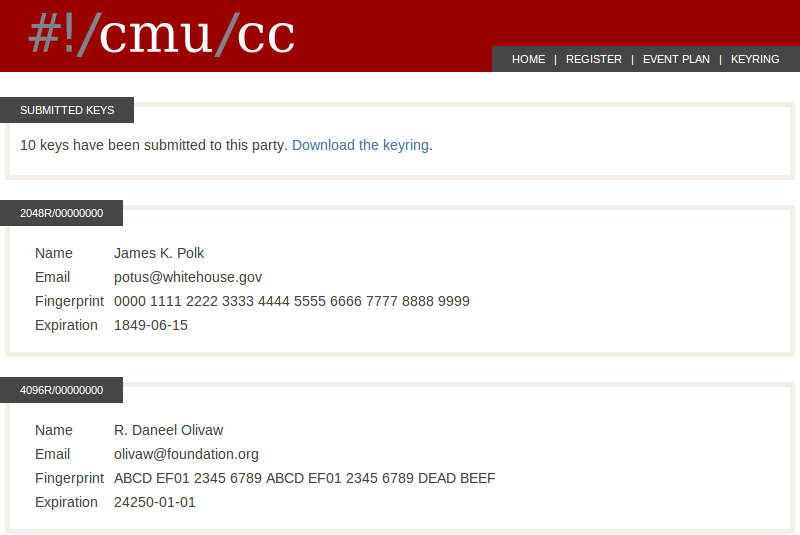
Keystorm is a solution to this mess. It is a keysigning party server, and as such possesses exactly the features necessary for the task, and scarce more. Attendees upload their ASCII-armored keys which are then processed by gpg server-side and stored in a local MongoDB instance. This allows us to generate a complete summary of the keys on the fly and also make available an up-to-date keyring for download.
Keystorm is implemented in Node.js using Express, Mongoose, and Jade. You can check out the source on GitHub.